We now have an official Red Hat Security Blog, and you'll find all my future reports and discussions about security metrics there. In the meantime here are a few already published articles:
- How
Red Hat rates JBoss security flaws
- CWE
Vulnerability Assessment Report
- Welcome to the Red Hat Security Blog
 The Common Vulnerability Reporting Framework (CVRF) is a way to share
information about security updates in an XML machine-readable format. CVRF
1.1 got released this week and over at Red Hat we've started publishing
our security advisories in CVRF format.
The Common Vulnerability Reporting Framework (CVRF) is a way to share
information about security updates in an XML machine-readable format. CVRF
1.1 got released this week and over at Red Hat we've started publishing
our security advisories in CVRF format.
Find out more
from our FAQ
and formatting
guide.
Red Hat Enterprise Linux 5.8 was released today (February 2012), seven months since the release of 5.7 in July 2011. So let's use this opportunity to take a quick look back over the vulnerabilities and security updates made in that time, specifically for Red Hat Enterprise Linux 5 Server.
Red Hat Enterprise Linux 5 is coming up to its fifth year since release, and is supported for another five years, until 2017.
Errata count
The chart below illustrates the total number of security updates issued for Red Hat Enterprise Linux 5 Server if you had installed 5.7, up to and including the 5.8 release, broken down by severity. It's split into two columns, one for the packages you'd get if you did a default install, and the other if you installed every single package (which is unlikely as it would involve quite a bit of manual effort to select every one). For a given installation, the number of package updates and vulnerabilities that affected you will depend on exactly what packages you have installed or removed.

So, for a default install, from release of 5.7 up to and including 5.8, we shipped 42 advisories to address 118 vulnerabilities. 4 advisories were rated critical, 13 were important, and the remaining 25 were moderate and low.
Or, for all packages, from release of 5.7 up to and including 5.8, we shipped 71 advisories to address 177 vulnerabilities. 7 advisories were rated critical, 16 were important, and the remaining 48 were moderate and low.
Critical vulnerabilities
The 7 critical advisories addressed 20 critical vulnerabilities across 4 different packages:
- An update to OpenJDK 6 Java Runtime Environment, (October 2011) where a web site hosting a malicious Java applet could potentially run arbitrary code as the user.
- An update to the MIT krb5 telnet daemon (December 2011) where a remote attacker who can access the telnet port of a target machine could use this flaw to execute arbitrary code as root. Note that the krb5 telnet daemon is not installed or enabled by default, and the default firewall rules block remote access to the telnet port. This flaw did not affect the more commonly used telnet daemon distributed in the telnet-server package.
- Updates to PHP and PHP 5.3 (February 2012) where a remote attacker could send a specially-crafted HTTP request to cause the PHP interpreter to crash or, possibly, execute arbitrary code. This flaw was caused by the fix for CVE-2011-4885.
- Three updates to Firefox (August 2011, September 2011, November 2011) where a malicious web site could potentially run arbitrary code as the user running Firefox.
Updates to correct 19 out of the 20 critical vulnerabilities were available via Red Hat Network either the same day or the next calendar day after the issues were public. The update to krb5 took 2 calendar days because it was public on Christmas day.
Overall, for Red Hat Enterprise Linux 5 since release until 5.8, 98% of critical vulnerabilities have had an update available to address them available from the Red Hat Network either the same day or the next calendar day after the issue was public.
Other significant vulnerabilities
Although not in the definition of critical severity, also of interest during this period were a couple of remote denial of service flaws that were easily exploitable:
- A flaw in BIND, CVE-2011-4313, fixed by RHSA-2011:1458 (bind) and RHSA-2011:1459 (bind97). A remote attacker could use this flaw to cause BIND to crash.
- A flaw in Apache HTTP Server, CVE-2011-3192, fixed by RHSA-2011:1245. A remote attacker could use this flaw to cause httpd to use an excessive amount of memory and CPU time.
In addition, updates to Firefox, NSS, and Thunderbird were made to blacklist a compromised Certificate Authority.
Previous update releases
To compare these statistics with previous update releases we need to take into account that the time between each update release is different. So looking at a default installation and calculating the number of advisories per month gives the following chart:

This data is interesting to get a feel for the risk of running Enterprise Linux 5 Server, but isn't really useful for comparisons with other major versions, distributions, or operating systems -- for example, a default install of Red Hat Enterprise Linux 4AS did not include Firefox, but 5 Server does. You can use our public security measurement data and tools, and run your own custom metrics for any given Red Hat product, package set, timescales, and severity range of interest.
See also: 5.7, 5.6, 5.5, 5.4, 5.3, 5.2, and 5.1 risk reports.
The inspiration for the Sonik video for Gravitation came from a local friend of ours, a talented and world-renowned photographer, Adrian Brannan. Ade is famous for his analogue photo collages (please give him a 'like' on his Facebook page):
We often wondered how the same effect would look if rendered with video. With video you've got the extra element of time, each segment of the mosaic can be running from a different starting point, with a different speed, and even a different direction. In addition the segments themselves can move over time. Would this end up with an effect that was just too much of a mess? Or would it give an effect that helps visualise the consequence of spacetime?
We started by taking several videos at three different locations over the period of a year with a Kodak Zi8 camera. A motorway bridge over the M74, just outside the Buchanan shopping center in Glasgow, and a bench in Strathclyde park. Lining up the images was done roughly by using lines drawn on acetate stuck over the camera screen.
The software to do the mosaic effect was hand-written. We used a simple scripting language, Perl, and the image library GD. On a relatively modern Linux PC running Fedora 16 we can render near real-time 720p HD even when handling 300 segments of mosaic. A simple language controls which parts of the screen come from which video, and the first half of the music video uses this with simple effects having just a few boxes overlayed:

Later in the video things get more complicated, using randomisation to pick the location and movement of each segment:

We used our scripts to create a number of ~13 second segments, then put them all together using kdenlive. The intro and outro were taken from a different video from a hotel room in London Victoria; the intro using a 'miniature' effect, and outro using the randomised segments applied to a single video.
The Perl script and a 5 frame example is available to download: 2011-sonik-vid-example.tar.bz2 (1.4M)
Watch the full video, or click through to YouTube to see it in HD:
Red Hat Enterprise Linux 6.2 was released this week (Dec 2011), just over six months since the release of 6.1 in May 2011. So let's use this opportunity to take a quick look back over the vulnerabilities and security updates made in that time, specifically for Red Hat Enterprise Linux 6 Server.
Errata count
The chart below illustrates the total number of security updates issued for Red Hat Enterprise Linux 6 Server if you had installed 6.1, up to and including the 6.2 release, broken down by severity. It's split into two columns, one for the packages you'd get if you did a default install, and the other if you installed every single package (which is unlikely as it would involve a bit of manual effort to select every one). For a given installation, the number of package updates and vulnerabilities that affected you will depend on exactly what you have installed or removed.
So, for a default install, from release of 6.1 up to and including 6.2, we shipped 36 advisories to address 121 vulnerabilities. 2 advisories were rated critical, 10 were important, and the remaining 24 were moderate and low.
Or, for all packages, from release of 6.1 up to and including 6.2, we shipped 88 advisories to address 218 vulnerabilities. 10 advisories were rated critical, 16 were important, and the remaining 62 were moderate and low.
Critical vulnerabilities
The 10 critical advisories addressed 31 critical vulnerabilities across 3 components:
- Two updates to the OpenJDK 6 Java Runtime (June 2011, October 2011) where a malicious web site presenting a Java applet could potentially run arbitrary code as the user running a web browser.
- Four updates to Firefox (June 2011, August 2011, September 2011, November 2011) where a malicious web site could potentially run arbitrary code as the user running Firefox.
- Four updates to Thunderbird (June 2011, August 2011, September 2011 November 2011) where a malicious email message could potentially run arbitrary code as the user running Thunderbird.
Updates to correct all of the 31 critical vulnerabilities were available via Red Hat Network either the same day or the next calendar day after the issues were public.
Other significant vulnerabilities
Although not in the definition of critical severity, also of interest during this period were a few flaws that were high risk or easily exploitable:
A flaw in Bind, CVE-2011-4313 fixed by RHSA-2011:1458 where a malicious client could cause Bind to stop responding, a denial of service attack. This flaw was discovered by it being accidentally triggered in the wild.
A flaw in the Apache HTTP Server, CVE-2011-3192, fixed by RHSA-2011:1245, where a remote attacker could cause a denial of service attack. This was discovered due to a public exploit.
A flaw in RPM, CVE-2011-3378 fixed by RHSA-2011:1349 where a specially-crafted RPM package that, when queried or installed, would cause rpm to crash or, potentially, execute arbitrary code prior to any signature checking. We're not aware of any working exploits for this issue.
Updates to blacklist the DigiNotar Certificate Authority.
Previous update releases
To compare these statistics with previous update releases we need to take into account that the time between each update release is different. So looking at a default installation and calculating the number of advisories per month gives the following chart:
This data is interesting to get a feel for the risk of running Enterprise Linux 6 Server, but isn't really useful for comparisons with other major versions, distributions, or operating systems -- for example, a default install of either Red Hat Enterprise Linux 4AS and 6 Server does not include Firefox, but a default install of 5 Server does. You can use our public security measurement data and tools, and run your own custom metrics for any given Red Hat product, package set, timescales, and severity range of interest.
When we get notified of a security issue affecting a Red Hat product in advance we give an acknowledgement in the security advisory and in our CVE database.
We've now created a page to give acknowledgements to the companies and individuals that report issues in our online services, such as finding a cross-site scripting flaw in a Red Hat web site, or a vulnerability in OpenShift.
We pushed an update to Flash Player for Red Hat Enterprise Linux Supplementary today, on a Friday, because it fixed Critical vulnerabilities. But we try not to push updates on a Friday unless they are critical and already public.
So let's take a look at the most common times and days we push advisories for Red Hat Enterprise Linux 4, 5, and 6 (including Supplementary) using a heatmap:
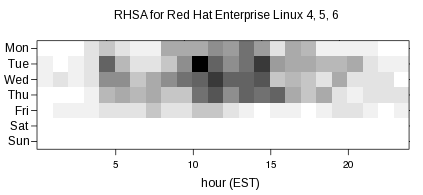
The more advisories pushed for a given date and hour, the darker that section of the graph is. So the most popular times for pushing advisories are Tuesdays at 10am and 2pm Eastern US time, Fridays are pretty light for pushes, and there was nothing during the weekends. The spread of the graph shows that we push advisories when they are ready, rather than waiting to a fixed day and time, in order to reduce the risk to users.
All the data used to create this graph is available as part of our public metrics. Thanks to Sami Kerola for the R code from which I based my graph generation.
 For my Birthday my wife bought me
a Peggy 2
kit, and I finally got around to adding the 625 10mm green LEDs. Some of the
example programs are pretty neat but I wanted to make a side scroller with
a nice font ready for halloween.
For my Birthday my wife bought me
a Peggy 2
kit, and I finally got around to adding the 625 10mm green LEDs. Some of the
example programs are pretty neat but I wanted to make a side scroller with
a nice font ready for halloween.
I decided on the Liberation Sans Narrow font, drew up a string of characters in The Gimp, converted it to have only 4 levels, then used a quick perl script to convert the image into program data for the scroller. I'm pretty happy with how it turned out. The scroller, image, and script are available here.
Every year since Red Hat Enterprise Linux 4 was released we've published a risk report where we look at the state of security of the distribution. We investigate the key vulnerabilities, metrics on vulnerability counts, and how users could have been exploited by them. The Six Years of Red Hat Enterprise Linux 4 report (PDF) covering Feb 2005-2011 was published today.
"Red Hat knew about 51.5% of the security vulnerabilities that we fixed in advance. The average time between Red Hat knowing about an issue and it being made public was 23 days (median 10 days).... A default installation of Red Hat Enterprise Linux 4 AS was vulnerable to 20 critical security issues over the first six years. "
The data we publish is interesting to get a feel for the risk of running Enterprise Linux, but isn't really useful for comparisons with other distributions, or operating systems. One important difference is that it is Red Hat policy to count vulnerabilities and allocate CVE names to all issues that we fix, including ones that are found internally. This is not true for many other vendors including folks like Microsoft and Adobe who do not count or disclose issues they fix which were found internally.
A few weeks ago the 2011 update to the CWE/SANS Top 25 Most Dangerous Software Errors was published. As part of our contribution to this update we analysed the most severe vulnerabilities that affected Red Hat since the last update and mapped each one to the appropriate Common Weakness Enumeration (CWE) type.
The table below lists all vulnerabilities which have a CVSS score of 7 or more ('high'), that we fixed in any product during calendar year 2010.
Most common CWE were:
- Buffer Copy without Checking Size of Input (CWE-120): 8 vulnerabilities.
- Race Condition (CWE-362): 5 vulnerabilities.
| CVE | CWE | 2011 top 25? | CVSS base score | Fixed in |
|---|---|---|---|---|
| CVE-2007-4567 | CWE-476 | no | 7.8 | Red Hat Enterprise Linux 5 (kernel) |
| CVE-2009-0778 | CWE-770 | no | 7.1 | Red Hat Enterprise Linux 5 (kernel) |
| CVE-2009-1385 | CWE-191 | no | 7.1 | Red Hat Enterprise Linux 5 (kernel) |
| CVE-2009-3080 | CWE-129 | no | 7.2 | Red Hat Enterprise Linux 3, 4, 5, MRG (kernel) |
| CVE-2009-3245 | CWE-252 | no | 7.6 | Red Hat Enterprise Linux 3, 4, 5 (openssl) |
| CVE-2009-3726 | CWE-476 | no | 7.2 | Red Hat Enterprise Linux 4, 5, MRG (kernel) |
| CVE-2009-4005 | CWE-127 | no | 7.1 | Red Hat Enterprise Linux 4 (kernel) |
| CVE-2009-4027 | CWE-362 | no | 7.8 | Red Hat Enterprise Linux 5 (kernel) |
| CVE-2009-4141 | CWE-416 | no | 7.2 | Red Hat Enterprise Linux 5, MRG (kernel) |
| CVE-2009-4212 | CWE-191 | no | 10.0 | Red Hat Enterprise Linux 3, 4, 5 (krb5) |
| CVE-2009-4272 | CWE-764 | no | 7.8 | Red Hat Enterprise Linux 5 (kernel) |
| CVE-2009-4273 | CWE-78 | yes | 7.9 | Red Hat Enterprise Linux 5 (systemtap) |
| CVE-2009-4537 | CWE-120 | yes | 7.1 | Red Hat Enterprise Linux 4, 5, MRG (kernel) |
| CVE-2009-4895 | CWE-362 | no | 7.2 | Red Hat Enterprise MRG (kernel) |
| CVE-2010-0008 | CWE-606 | no | 7.8 | Red Hat Enterprise Linux 4, 5 (kernel) |
| CVE-2010-0291 | CWE-822 | no | 7.2 | Red Hat Enterprise Linux 5 (kernel) |
| CVE-2010-0738 | CWE-424 | no | 7.5 | JBoss Enterprise Application Platform 4.2, 4.3 |
| CVE-2010-0741 | CWE-20 | no | 7.1 | Red Hat Enterprise Linux 5 (kvm) |
| CVE-2010-1084 | CWE-120 | yes | 7.2 | Red Hat Enterprise Linux 5 (kernel) |
| CVE-2010-1086 | CWE-20 | no | 7.8 | Red Hat Enterprise Linux 4, 5 (kernel) |
| CVE-2010-1087 | CWE-362 | no | 7.2 | Red Hat Enterprise Linux 5 (kernel) |
| CVE-2010-1166 | CWE-823 | no | 7.6 | Red Hat Enterprise Linux 5 (xorg-x11-server) |
| CVE-2010-1173 | CWE-120 * | yes | 7.1 | Red Hat Enterprise Linux 4, 5 (kernel) |
| CVE-2010-1188 | CWE-416 | no | 7.8 | Red Hat Enterprise Linux 3, 4, 5 (kernel) |
| CVE-2010-1436 | CWE-120 | yes | 7.2 | Red Hat Enterprise Linux 5 (kernel) |
| CVE-2010-1437 | CWE-362 | no | 7.2 | Red Hat Enterprise Linux 4, 5 (kernel) |
| CVE-2010-2063 | CWE-823 | no | 7.5 | Red Hat Enterprise Linux 3, 4, 5 (samba) |
| CVE-2010-2235 | CWE-77 | no | 7.1 | Red Hat Network Satellite Server 5.3 (cobbler) |
| CVE-2010-2240 | CWE-788 | no | 7.2 | Red Hat Enterprise Linux 3, 4, 5, MRG (kernel) |
| CVE-2010-2248 | CWE-682 | no | 7.1 | Red Hat Enterprise Linux 4, 5 (kernel) |
| CVE-2010-2492 | CWE-805 | no | 7.2 | Red Hat Enterprise Linux 5, 6 (kernel) |
| CVE-2010-2521 | CWE-805 | no | 8.3 | Red Hat Enterprise Linux 4, 5, MRG (kernel) |
| CVE-2010-2798 | CWE-476 | no | 7.2 | Red Hat Enterprise Linux 5 (kernel) |
| CVE-2010-2962 | CWE-823 | no | 7.2 | Red Hat Enterprise Linux 6, MRG (kernel) |
| CVE-2010-3069 | CWE-129 | no | 8.3 | Red Hat Enterprise Linux 3, 4, 5, 6 (samba) |
| CVE-2010-3081 | CWE-131 | yes | 7.2 | Red Hat Enterprise Linux 3, 4, 5, 6, MRG (kernel) |
| CVE-2010-3084 | CWE-120 | yes | 7.2 | Red Hat Enterprise Linux 6 (kernel) |
| CVE-2010-3301 | CWE-129 | no | 7.2 | Red Hat Enterprise Linux 6 (kernel) |
| CVE-2010-3302 | CWE-120 | yes | 7.1 | Red Hat Enterprise Linux 6 (openswan) |
| CVE-2010-3308 | CWE-120 | yes | 7.1 | Red Hat Enterprise Linux 6 (openswan) |
| CVE-2010-3432 | CWE-805 * | no | 7.8 | Red Hat Enterprise Linux 4, 5, 6, MRG (kernel) |
| CVE-2010-3705 | CWE-788 | no | 8.3 | Red Hat Enterprise Linux 6, MRG (kernel) |
| CVE-2010-3708 | CWE-77 | no | 7.5 | JBoss Enterprise Application Platform 4.3, SOA Platform 4.2 |
| CVE-2010-3752 | CWE-78 | yes | 7.1 | Red Hat Enterprise Linux 6 (openswan) |
| CVE-2010-3753 | CWE-78 | yes | 7.1 | Red Hat Enterprise Linux 6 (openswan) |
| CVE-2010-3847 | CWE-426 | no | 7.2 | Red Hat Enterprise Linux 5, 6 (glibc) |
| CVE-2010-3856 | CWE-426 | no | 7.2 | Red Hat Enterprise Linux 5, 6 (glibc) |
| CVE-2010-3864 | CWE-362 | no | 7.6 | Red Hat Enterprise Linux 6 (openssl) |
| CVE-2010-3904 | CWE-822 | no | 7.2 | Red Hat Enterprise Linux 5, 6 (kernel) |
| CVE-2010-4170 | CWE-88 | no | 7.2 | Red Hat Enterprise Linux 4, 5, 6 (systemtap) |
| CVE-2010-4179 | CWE-862 | yes | 7.5 | Red Hat Enterprise MRG (cumin) |
| CVE-2010-4344 | CWE-120 | yes | 7.5 | Red Hat Enterprise Linux 4, 5 (exim) |
* - in both these cases the outcome is not a buffer overflow as the possible overflow is detected and instead converted into an abort (DoS)
See also our 2010 analysis